- All of Microsoft

Guide: Check MFA Status for Each User in Entra with Graph
Discover Microsoft Graph PowerShell for Reporting Per-User MFA Status in Microsoft Entra!
Key insights
- Learn how to utilize Microsoft Graph PowerShell to view the per-user MFA state and method for users in Microsoft Entra.
- The Microsoft Graph API is evolving to match features with the Azure Graph API, including the ability to view per-user MFA status.
- Per-user MFA allows configuration and enforcement on a per-user basis within the legacy admin panel, although it is advisable to switch to Conditional Access.
- To access per-user MFA settings with PowerShell, use the Beta Microsoft Graph endpoint and appropriate modules.
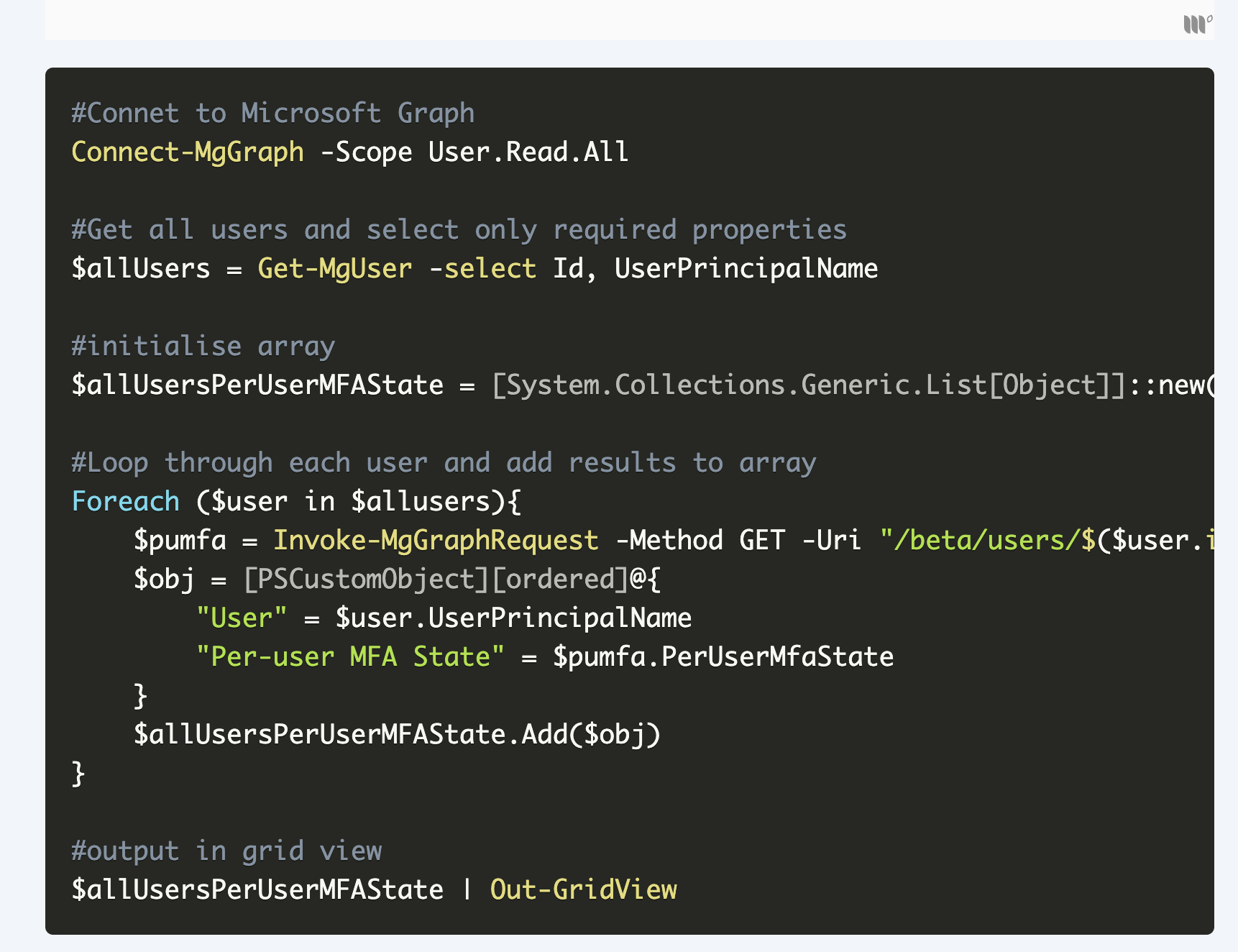
- A PowerShell script can retrieve a list of all users and their per-user MFA status, displaying it in a popup grid view.
Understanding Per-User MFA in Microsoft Entra
In terms of enhancing security within Microsoft Entra, understanding the mechanisms behind per-user Multi-Factor Authentication (MFA) is crucial. The traditional per-user MFA approach, where each user's multi-factor authentication settings are individually managed and enforced, is now considered somewhat legacy. Modern best practices recommend a migration towards more dynamic and secure authentication strategies, such as Conditional Access.
This strategy aligns with a shift in administrative tools and approaches, where Microsoft's Graph PowerShell plays an integral role. It not only allows administrators to manage these settings more efficiently but also ensures a smoother migration to more robust security mechanisms. The PowerShell interface, coupled with Microsoft Graph API, provides the flexibility and control needed by IT teams to manage user authentications on a granular level.
The transition to such modern methods, though, requires understanding the intricate details and configurations available in Entra's admin portal. With security threats becoming more sophisticated, upgrading to conditional access systems is imperative for protecting sensitive data and maintaining user trust.
Read the full article Report per-user MFA status in Entra using Microsoft Graph PowerShell

Learn how to use Microsoft Graph PowerShell to report the per-user MFA status and method for users in Entra. This information is crucial for understanding user authentication security settings within the Microsoft Entra environment.
The post discusses the Microsoft Graph API’s features, emphasizing its capabilities in viewing MFA statuses to aid migration to more secure systems like Conditional Access. This capability was not available before June 2024 in its predecessor, the Azure Graph API.
It explains that in Microsoft Entra, some legacy MFA settings still exist. These settings, known as per-user MFA, let administrators configure MFA on a per-user basis. However, admins are encouraged to switch to Conditional Access for a better authentication experience.
The article details the steps necessary to access per-user MFA settings in the Entra admin portal. Users need to log in, navigate to Users > All Users, and select per-user MFA.
As of June 2023, per-user MFA settings are accessible only through the Beta endpoint of Microsoft Graph. To exploit this capability, several specific modules must be installed, including Microsoft.Graph.Authentication and optionally Microsoft.Graph.Beta.Users.
To view the per-user MFA status for all users, a PowerShell script is demonstrated. This script retrieves all users, reviews their per-user MFA settings, and organizes this data into an array, which can then be displayed in a grid view.
- The evolution of Microsoft Graph in catching up feature-wise with Azure Graph API.
- Details on accessing per-user MFA settings through the Entra admin portal.
- The required modules and permissions for utilizing Microsoft Graph with PowerShell.
- Steps to execute a PowerShell script to fetch and display per-user MFA states for Entra users.
The blog post effectively conveys the necessary steps and scripts to utilize Microsoft Graph for monitoring and enforcing multi-factor authentication (MFA) at a granular level. It provides detailed instructions and background, making it a valuable resource for IT admins and cybersecurity professionals seeking to enhance their user authentication mechanisms.
Further Insight into Per-User MFA Using Microsoft Graph
Implementing per-user multi-factor authentication (MCA) in Microsoft Entra through Microsoft Graph is a critical aspect of modern cybersecurity frameworks. This approach not only underpins robust security protocols but also highlights the shift towards more secure, user-specific controls in enterprise environments. Transitioning to Conditional Access, as advocated, optimizes the authentication process, minimizes potential entry points for cybersecurity threats, and ensures a seamless user experience. The detailed guides and scripts provided in the post are invaluable for administrators looking to enhance their security architecture with up-to-date, effective security measures using Microsoft Graph.
People also ask
How to report the MFA status for Entra ID user account?
The first method involves using the Microsoft Entra Admin Center.
How do I check MFA status for a user in PowerShell?
Begin by launching PowerShell and connecting to MS Graph. Input the script's path and name to run it. This script will enumerate how many accounts it locates and indicate which account is currently being processed. Upon completion, it will display the MFA status and authentication methods for each user.
How to get a list of users with MFA disabled?
To find users with MFA disabled, specific queries or commands would typically be used within your management platform to filter these users out from your database.
What is the MFA usage report?
The MFA Usage report details a list that includes all authenticator enrollments, based on authentication activity from users when they log into their accounts.
Keywords
Report per-user MFA status, Entra MFA report, Microsoft Graph PowerShell, MFA status PowerShell, Entra security reporting, PowerShell MFA query, Entra PowerShell automation, Microsoft security PowerShell