- All of Microsoft

Disable User MFA with Microsoft Graph PS: Easy Guide
Master Microsoft Graph PowerShell: Disable MFA in Entra for Secure Migration!
Key insights
- Disabling per-user MFA using Microsoft Graph PowerShell allows for smooth migration to Conditional Access policies.
- As of June 2024, per-user MFA configurations can only be managed through the Beta endpoint of Microsoft Graph.
- Specific Microsoft Graph modules like Microsoft.Graph.Authentication and Microsoft.Graph.Users are essential for accessing and modifying per-user MFA settings.
- To disable MFA for a single user or multiple users, you must run specific PowerShell commands, specifying user IDs and setting the MFA state to disabled.
- Daniel Bradley, the author, is an experienced engineer and consultant in Microsoft 365 and Azure platforms, sharing technical insights with the community.
Understanding Per-User MFA and its Management through Microsoft Graph PowerShell
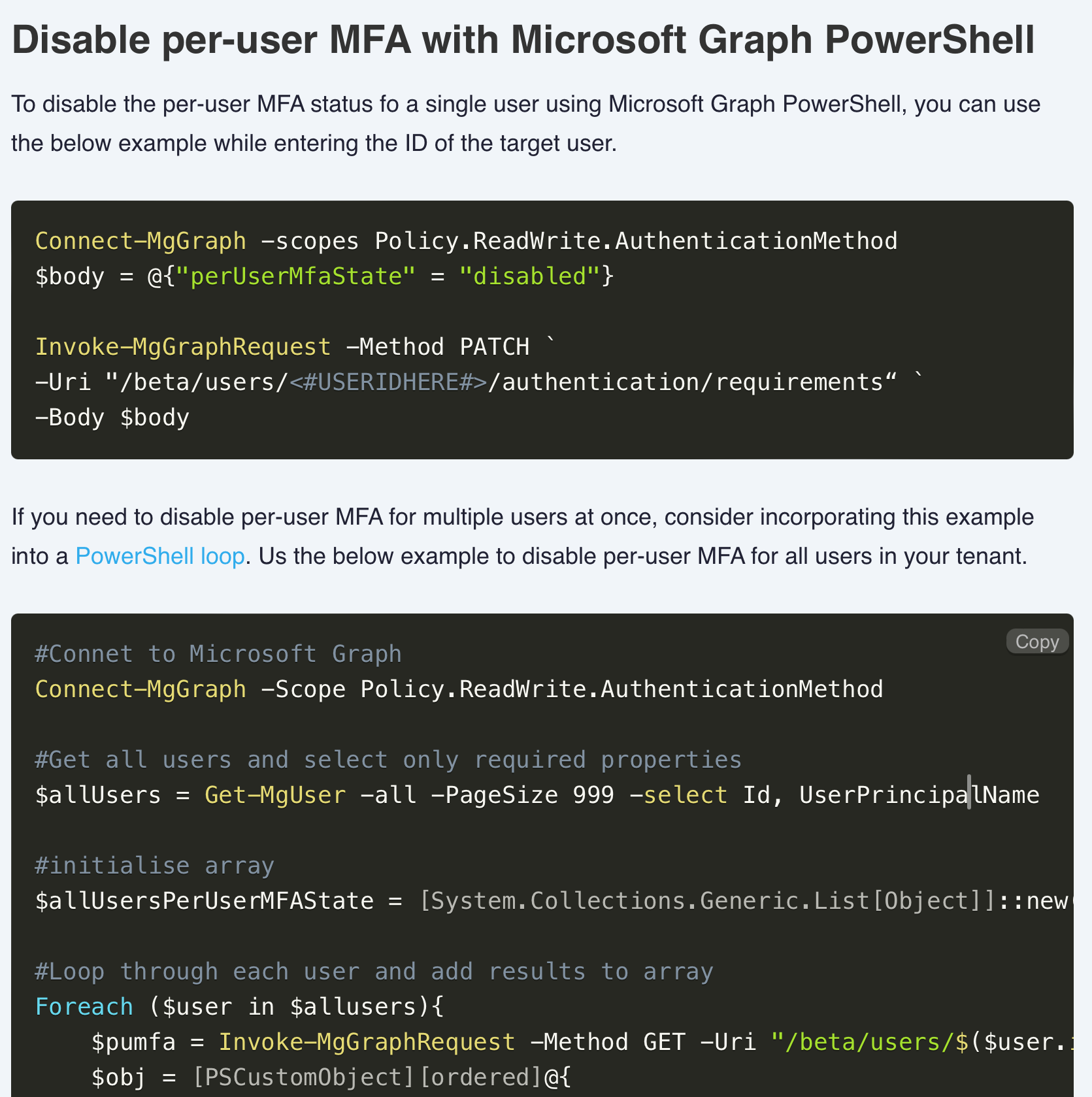
Learn about deactivating per-user multi-factor authentication (MFA) for Microsoft Entra users through a specific PowerShell tool. The blog post delves into scripting methods, providing instructions on disabling MFA for individual or multiple users.
This instruction kit requires the beta version of the Microsoft Graph endpoint as of June 2024. Essential for this process are specific PowerShell modules and admin consent for necessary user and policy permissions. Detailed steps, including command lines and parameters, support these requirements.
For example, to alter MFA settings for a single user, the PowerShell script utilizes a PATCH request with a specific user identifier, employing a predefined body to disable the MFA state. If intending to update MFA settings for multiple users, a loop function is recommended, aggregating user data and applying changes en masse.
- Use the Microsoft Graph PowerShell to change MFA settings.
- Commands need the beta Microsoft Graph endpoint.
- Global Administrator account is necessary for consent.
- Bulk updates can be managed through a loop, manipulating MFA for numerous users collectively.
Daniel Bradley, the author and an engineer specializing in Microsoft 365 and Azure, shares his personal insights in crafting user management scripts. Engaging with the community, he aims to facilitate technical understanding and implementation.
Read the full article How to disable per-user MFA using Microsoft Graph PowerShell

Microsoft Graph's Role in Managing Security Settings
Microsoft Graph plays a pivotal role in simplifying the management of security protocols within Microsoft’s ecosystem, particularly regarding identity services in Microsoft Entra. It extends administrators the capability to interact directly with various Microsoft services through a unified API, making it invaluable for managing complex tasks such as enabling or disabling Multi-Factor Authentication (MFA) for users.
Recognizing the significance of security in today's digital environment, Microsoft Graph offers robust support for automating security management tasks, thereby mitigating potential risks and enhancing the overall security posture of an organization. This streamlined access to services also supports the migration to more advanced security measures like Conditional Access, demonstrating Microsoft’s commitment to providing sophisticated tools for administering and securing user identities. By integrating these functions within a flexible and powerful interface, Microsoft Graph ensures administrators can effectively enforce security measures tailored to their organization’s specific needs.
People also ask
How do I disable Microsoft MFA per user?
To disable Multi-Factor Authentication (MFA) on a per-user basis, simply navigate to each individual user's settings and turn off the MFA option.
How to disable MFA for a user using PowerShell?
When managing MFA settings via PowerShell, first establish a connection with your Azure Active Directory (Azure AD). Utilize the Set-AzureADUser cmdlet to modify the MFA settings for a particular user. Use this command by replacing “user@abcd.com” with the user’s UPN (User Principal Name) who requires MFA to be disabled.
How do I turn off MFA for one user?
Disabling MFA for an individual user can be done through the Microsoft 365 admin center. Navigate to Users -> Active users, select the intended user, click on Manage multifactor authentication, and then disable MFA for that user.
How do I exclude a user from MFA?
To exclude a user from MFA, access the Assignments section and select Users and Groups. In the Include settings, opt for All users, but in the Exclude settings, select a pre-defined group like “MFA Excluded Users”. For applications, you can either cover All Cloud apps or just the Microsoft 365 apps as required.
Keywords
Disable MFA Microsoft Graph PowerShell, Disable Per-User MFA PowerShell, Microsoft Graph Disable MFA, Manage MFA PowerShell Microsoft, Disable Multi-Factor Authentication PowerShell, Use Microsoft Graph for MFA Settings, PowerShell Script to Disable MFA, Disable User MFA Microsoft Graph